Microsoft Teams External Domains Anomalies Report Security Feature
Microsoft is introducing a new security feature for its Teams collaboration platform called the "External Domains Anomalies Report," aimed at enhancing the detection of suspicious or risky interactions with external organizations. This tool, scheduled for rollout in February 2026, will provide IT administrators with behavioral analytics to identify unusual communication patterns, such as sudden spikes in message volume to specific external domains or interactions with previously unseen domains. The feature is designed to address the growing security challenges posed by increased external collaboration and remote work, offering actionable intelligence to help prevent data leaks, social engineering attacks, and unauthorized use of third-party services.
The report will be available for standard multi-tenant cloud environments via the Teams web platform and will help organizations maintain a balance between productive cross-organization work and robust data protection. In addition to this new reporting capability, Microsoft continues to enhance Teams' security posture by warning users about malicious links, improving protections against unsafe file types, and introducing features to block unauthorized screen captures and streamline client performance. The External Domains Anomalies Report represents a proactive step in giving administrators early visibility into potential threats arising from external communications.
Timeline
Feb 1, 2026
Microsoft schedules Teams anomaly report rollout for February 2026
Microsoft said the External Domains Anomalies Report is planned for release in February 2026 for Teams on Worldwide Standard Multi-Tenant cloud instances via the web platform.
Dec 10, 2025
Microsoft announces Teams External Domains Anomalies Report
Microsoft introduced a new Teams security feature called the External Domains Anomalies Report, designed to help administrators detect unusual communication patterns with external domains that could indicate threats such as data exfiltration or compromised accounts.
See the full picture in Mallory
Mallory subscribers get deeper analysis on every story, including:
Who’s affected and how
Deep-dive technical analysis
Actionable next steps for your team
IPs, domains, hashes, and more
Ask questions and take action on every story
Filter by topic, classification, timeframe
Get matching stories delivered automatically
Related Entities
Organizations
Sources
Related Stories
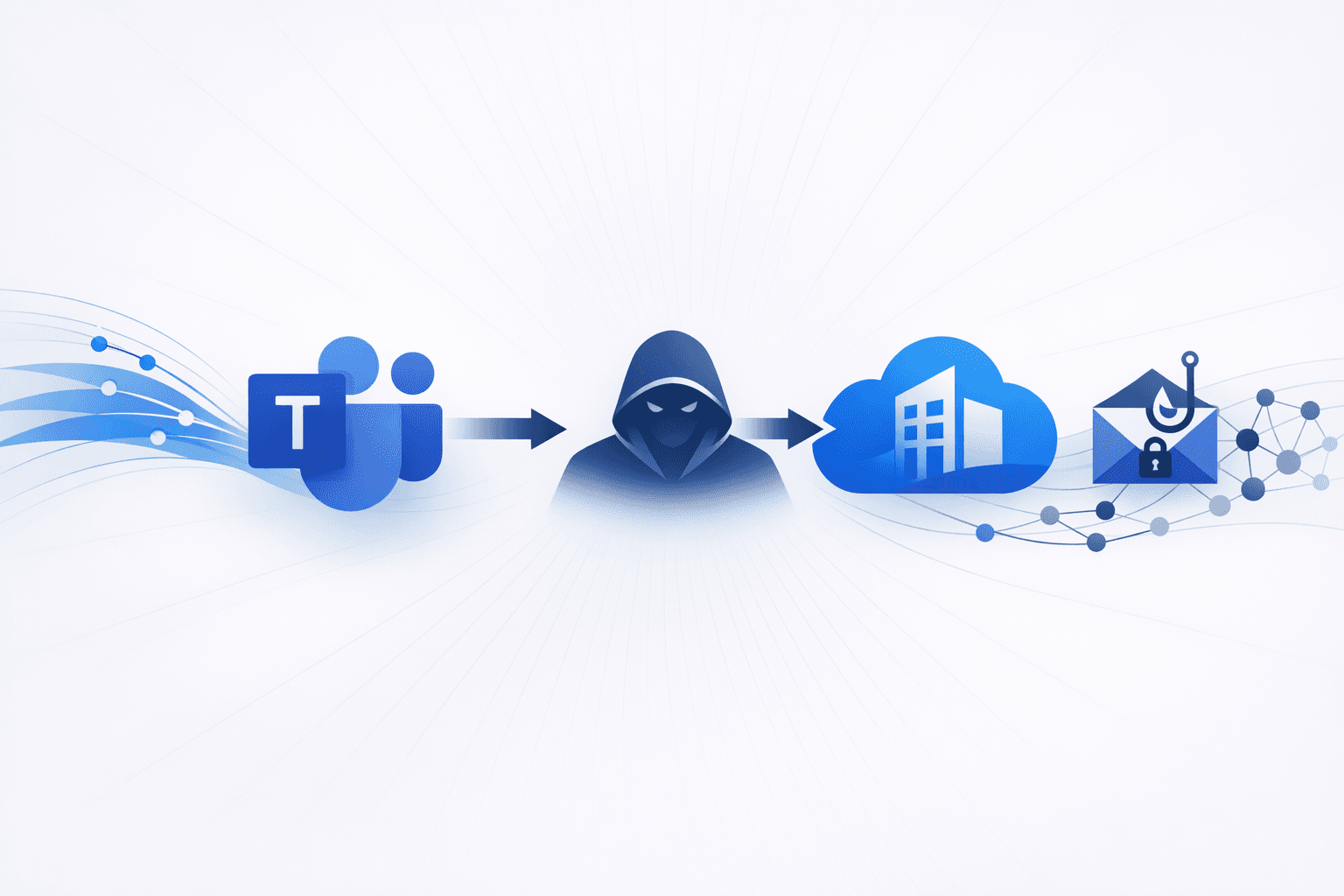
Microsoft Teams and Azure Tenant Abuse for Social Engineering Attacks
Microsoft is introducing a new feature that allows security administrators to block external users from sending messages, calls, or meeting invitations to their organization via Teams, managed through the Microsoft Defender portal. This integration with Defender for Office 365 enables admins to centrally manage blocked external contacts, supporting up to 4,000 domains and 200 email addresses, and is designed to counteract cybercrime groups, including ransomware actors, who exploit Teams for social engineering. The update will also enhance default security by enabling malicious URL detection and warning admins about suspicious external traffic, aiming to strengthen organizational defenses against external threats. Simultaneously, cybercriminals are exploiting legitimate Microsoft infrastructure, specifically `.onmicrosoft.com` domains assigned to Azure tenants, to launch Telephone-Oriented Attack Delivery (TOAD) scams. Attackers create controlled tenants and send malicious invites that appear to originate from trusted Microsoft addresses, bypassing standard email security filters. These invites contain social engineering lures in the message field, urging recipients to call fraudulent support numbers. Security teams are advised to implement targeted Exchange Transport Rules using Regex to mitigate this threat, as blocking the entire domain would disrupt legitimate operations.
1 months ago
Microsoft Teams to Enforce Messaging Safety Defaults
Microsoft is set to automatically enable key messaging safety features in Microsoft Teams for tenants using default configurations, starting January 12, 2026. The update will activate protections against weaponizable file types, real-time malicious URL detection, and a reporting mechanism for false positives, aiming to reduce the risk of malware and phishing attacks within enterprise collaboration environments. Organizations that have previously customized their messaging safety settings will not be affected by this change, as their preferences will remain in place. End-users will experience changes such as warning labels on suspicious URLs and blocked messages when attempting to share high-risk file types. The reporting feature allows users to flag incorrect security detections, helping Microsoft refine its threat detection algorithms. IT administrators are advised to review and update their Teams configurations and internal documentation before the rollout to ensure a smooth transition and maintain desired security postures.
1 months ago
Microsoft 365 message security changes: Teams user reporting expansion and Exchange Online false-positive quarantines
Microsoft is expanding end-user reporting capabilities in **Microsoft Teams** by enabling **Defender for Office 365 Plan 1** customers to report suspicious messages directly in Teams (Roadmap ID `531760`), a capability previously limited to Plan 2. The feature is intended to strengthen collaboration-platform defenses by letting users classify messages as **Security Risk** (suspected phishing/malware/spam) or **Not a Security Risk** (false positives), providing additional signals to SOC workflows and improving detection for chat-based social engineering such as **BEC-style** lures delivered via Teams; the rollout is expected to complete by late March 2026 and requires administrative enablement. Separately, Microsoft acknowledged an **Exchange Online** service issue in which legitimate emails were incorrectly marked as phishing/spam and quarantined, disrupting some users’ ability to send/receive email. Microsoft attributed the false positives to a **new URL rule** that misclassified certain legitimate URLs/domains as malicious due to evolving detection criteria; some previously quarantined messages may begin reappearing as mitigations roll out, but other emails may remain quarantined until the fix is fully deployed, and affected organizations are advised to review quarantine for missing legitimate mail.
1 months ago