Kimsuky Delivers DocSwap Android Malware via QR Code Phishing Impersonating Delivery Services
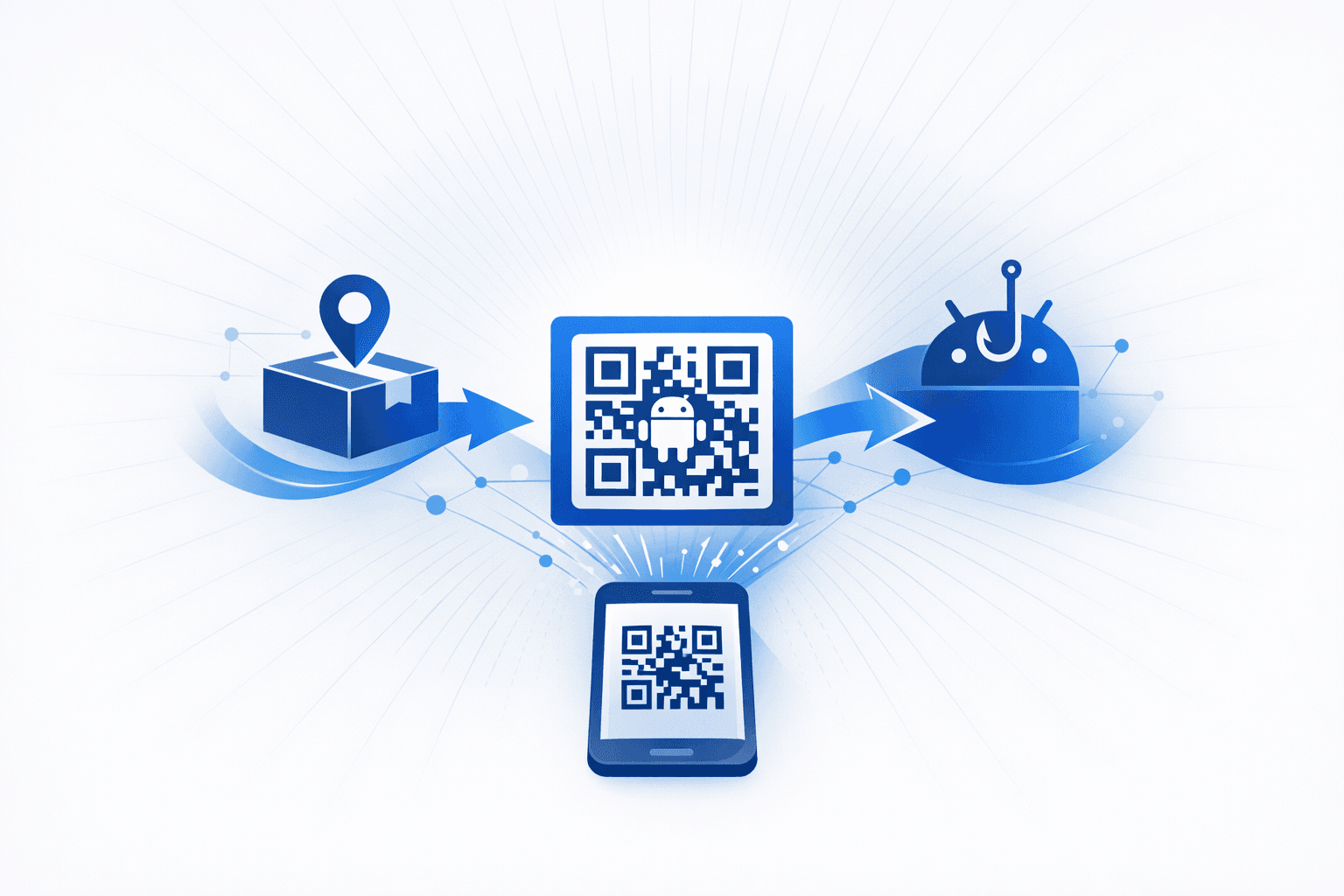
The North Korean state-sponsored threat group Kimsuky has launched a sophisticated campaign distributing a new variant of the DocSwap Android malware. Attackers use phishing sites that impersonate legitimate delivery services, particularly Seoul-based CJ Logistics, to lure victims. The campaign leverages QR codes and notification pop-ups to trick users into installing a malicious APK, often named SecDelivery.apk, on their mobile devices. Victims are typically targeted through smishing messages or phishing emails containing links to these fake delivery tracking sites. When accessed from a desktop, the site displays a QR code, prompting users to scan it with their Android device, which then initiates the malware download. The malicious app decrypts an embedded encrypted APK and launches a service with remote access trojan (RAT) capabilities, requesting extensive permissions to access files, SMS, phone, and location data.
Security researchers have observed that the campaign employs advanced evasion techniques, such as device-type detection and server-side logic to serve different content based on the user's platform. The malware variant features improvements over previous DocSwap versions, including a new native decryption function and enhanced decoy behaviors. The infrastructure supporting the campaign is linked to a command and control server at 27.102.137[.]181, and the phishing lures are designed to bypass Android's default security warnings by impersonating official apps and security modules. This campaign highlights the evolving tactics of Kimsuky in targeting South Korean users and the growing threat of QR code-based phishing for mobile malware delivery.
Timeline
Dec 18, 2025
Researchers link campaign to Kimsuky and reveal additional trojanized apps
Public reporting tied the campaign to Kimsuky based on shared infrastructure and Korean-language code comments, and disclosed related samples masquerading as P2B Airdrop and BYCOM VPN apps. Researchers also identified command-and-control infrastructure and documented the malware's extensive remote command set.
Dec 17, 2025
Kimsuky deploys updated DocSwap malware via fake delivery sites
Kimsuky distributed an updated DocSwap Android malware variant through phishing pages impersonating delivery services, including CJ Logistics. The malware used enhanced decryption, decoy behavior, persistence mechanisms, and broad RAT capabilities for surveillance and data theft.
Sep 1, 2025
Kimsuky mobile malware campaign first detected
A new Kimsuky campaign targeting Android users was first detected in September 2025. The operation used smishing, phishing sites, and weaponized QR codes to lure victims into installing malware disguised as delivery or security-related apps.
See the full picture in Mallory
Mallory subscribers get deeper analysis on every story, including:
Who’s affected and how
Deep-dive technical analysis
Actionable next steps for your team
IPs, domains, hashes, and more
Ask questions and take action on every story
Filter by topic, classification, timeframe
Get matching stories delivered automatically
Related Entities
Threat Actors
Malware
Organizations
Sources
Related Stories

Kimsuky APT Quishing Attacks Targeting Microsoft 365 and Google Workspace
The FBI, CISA, and NSA have issued warnings about a surge in spear-phishing campaigns conducted by the North Korean state-sponsored threat group Kimsuky (APT43), which leverage malicious QR codes—known as quishing—to target high-value individuals in government, academia, think tanks, and foreign policy organizations. These attacks embed QR codes in phishing emails, which, when scanned, redirect victims to credential harvesting sites or initiate malware downloads, often bypassing traditional email security controls and exploiting the relative insecurity of mobile devices. Kimsuky’s campaigns are characterized by highly personalized lures, extensive reconnaissance, and a focus on intelligence gathering, with observed targeting of Microsoft 365 and Google Workspace accounts. Quishing attacks are effective because QR codes can evade standard email security measures such as URL inspection and sandboxing, and they obscure the true destination from the user. Once a victim scans the QR code, attackers can collect device and identity attributes, present mobile-optimized phishing pages impersonating legitimate portals (such as Microsoft 365 or Okta), and steal credentials or session tokens—sometimes bypassing multi-factor authentication. The campaigns have been observed globally and represent a significant evolution in Kimsuky’s social engineering and credential theft operations, prompting urgent mitigation guidance from U.S. federal agencies and security researchers.
1 months ago
Android Banking Trojans Spread via Fake Document Reader and KYC Apps
Researchers reported two Android banking malware campaigns using staged droppers to evade detection and steal financial data from mobile users. Zscaler ThreatLabz said a fake **Document Reader** app on Google Play was downloaded more than 10,000 times before removal and later fetched the **Anatsa** payload from a remote server, while CYFIRMA identified **KYCShadow** being distributed through fake KYC verification apps sent over WhatsApp to bank customers in India. In both cases, the initial apps appeared legitimate, then installed secondary malicious components designed to bypass early screening and analysis. Once deployed, the malware sought high-risk permissions to hijack accounts, intercept SMS-based one-time passwords, and overlay banking apps to capture credentials. Anatsa was reported to target more than **831 financial institutions** globally, including banks and cryptocurrency platforms, using obfuscation and anti-analysis techniques, while KYCShadow collected data such as mobile numbers, Aadhaar details, ATM PINs, and card information, then used Firebase Cloud Messaging and a full-tunnel VPN for command-and-control and traffic redirection. Researchers urged users to uninstall suspicious apps and avoid software delivered through messaging platforms, and advised defenders to monitor indicators including `jsonapi[.]biz`, `jsonserv[.]biz`, and `jsonserv[.]xyz`.
4 days ago
Phishing and Smishing Campaigns Delivering Malware via Fake Apps and Trusted-Looking Lures
Multiple reports describe **social-engineering campaigns** that use trusted-looking lures (meeting invites, public-safety alerts, and official-looking documents) to drive victims to install malware or disclose credentials. Microsoft researchers reported a wave of **fake Zoom/Teams/Adobe update sites** reached via meeting-invite and document lures; the downloaded executables were signed with a **compromised EV code-signing certificate** (issued to *TrustConnect Software PTY LTD*) and acted as droppers for **remote monitoring and management (RMM) tools**, enabling persistent access. Separately, ClearSky described a suspected **Russian espionage** phishing operation targeting Ukraine that delivers a ZIP containing a Ukrainian-language border-crossing “permit” document, installing a loader (**BadPaw**) and a backdoor (**MeowMeow**) with file manipulation capabilities and sandbox/VM evasion; attribution was assessed as high confidence to a Russian state-aligned actor and low confidence to **APT28**. Mobile-focused lures were also reported: CloudSEK detailed **SMS phishing** targeting Israeli civilians with a trojanized **Red Alert** rocket-warning app, using a multi-stage loader chain to deploy spyware with **banking trojan** capabilities and exfiltrate **SMS, contacts, and location** to attacker infrastructure—raising concerns about surveillance and erosion of trust in official alerting. Other items in the set are either broader research or consumer-oriented scam advisories: a Zimperium write-up on the Android **“Massiv”** IPTV-app disguise highlights overlay-based banking fraud techniques, while Kaspersky’s mobile threat landscape report provides 2025 ecosystem statistics; two OnlineThreatAlerts posts describe generic **smishing** patterns (Amazon “refund” and flood-warning texts) without tying to a specific, evidenced campaign or new technical findings.
1 months ago