Phishing campaigns abuse trusted platforms and authentication flows to evade detection and steal credentials
Multiple active phishing operations are leveraging trusted services and by-design web/authentication features to bypass security controls and harvest credentials and MFA data. GTFire is a large-scale credential-harvesting campaign that hides behind legitimate Google-owned domains by abusing Firebase and Google Translate to make phishing links appear trustworthy to email filters and web gateways; victims are sent to brand-impersonation login pages and then redirected to the real site after submitting credentials. Separately, Microsoft reported phishing that abuses OAuth redirection behavior in identity providers (including Microsoft Entra ID and Google Workspace) by registering malicious OAuth apps with attacker-controlled redirect URIs and using silent auth flows/invalid scopes to bounce users to attacker infrastructure; Microsoft disabled the identified malicious Entra OAuth applications but noted related activity continues and requires monitoring.
A distinct but thematically similar campaign uses a fake Google Account security site to trick users into installing a malicious Progressive Web App (PWA) that can steal one-time passcodes (via WebOTP where supported), harvest data (e.g., clipboard contents), and even turn the victim’s browser into an attacker-controlled proxy with internal port-scanning capability; Malwarebytes-linked reporting highlighted the lure domain google-prism[.]com and the use of permission prompts (notifications/clipboard) to enable ongoing abuse. Other items in the set cover unrelated threats (Android malware using generative AI for persistence, an Iraq-focused APT toolchain, a separate AiTM phishing-kit attribution case study, and research on a cybercrime infrastructure provider), and do not describe the same specific phishing operations described above.
Timeline
Mar 2, 2026
Group-IB exposed GTFire phishing infrastructure and stolen credentials
Group-IB reported that exposure of attacker-controlled GTFire command-and-control servers revealed thousands of stolen credentials linked to more than 1,000 organizations across over 100 countries and 200-plus industries, with Mexico the most affected. The campaign abused Google Translate and Google Firebase domains to host and relay credential-harvesting pages while rotating infrastructure to evade detection.
Mar 2, 2026
Campaign expanded with Android app posing as Google security update
Researchers found that some victims were also offered a companion Android APK disguised as a Google-verified critical security update. The app requested extensive permissions and included capabilities for keystroke capture, notification interception, credential theft, persistence, and possible overlay attacks.
Mar 2, 2026
Researchers documented fake Google security PWA phishing campaign
Malwarebytes reported a phishing campaign using a fake Google Account security page on google-prism[.]com to trick users into installing a malicious Progressive Web App. The PWA was designed to steal one-time passcodes, collect sensitive data, harvest cryptocurrency wallet addresses, and proxy attacker traffic through victims' browsers.
Mar 2, 2026
Microsoft disabled malicious OAuth applications tied to the campaigns
During its investigation, Microsoft Entra disabled the malicious OAuth applications observed in the redirect-abuse campaigns. Microsoft said related activity was still continuing and required ongoing monitoring.
Mar 2, 2026
Microsoft observed OAuth redirect abuse in phishing and malware campaigns
Microsoft reported campaigns targeting government and public-sector organizations that abused standards-compliant OAuth redirection behavior to send victims from trusted identity provider domains to attacker-controlled phishing and malware infrastructure. The activity used silent OAuth flows and invalid scopes to trigger redirects without stealing OAuth tokens directly.
See the full picture in Mallory
Mallory subscribers get deeper analysis on every story, including:
Who’s affected and how
Deep-dive technical analysis
Actionable next steps for your team
IPs, domains, hashes, and more
Ask questions and take action on every story
Filter by topic, classification, timeframe
Get matching stories delivered automatically
Sources
Related Stories
Phishing Campaigns Abuse Trusted Platforms and Collaboration Tools to Steal Credentials
Multiple reports describe a broader **credential-theft trend** in which attackers abuse trusted services and familiar business workflows to make phishing more convincing and harder to detect. One campaign used **compromised WordPress sites** and redirects through `skimresources[.]com` to deliver pixel-perfect fake login pages for **Microsoft Teams**, **Xfinity**, and **UAE Pass**, with lures such as missed voicemail and shared-document alerts. Another campaign abused **LiveChat**'s `lc[.]chat` infrastructure to impersonate brands like **PayPal** and **Amazon**, moving victims into fake support conversations designed to extract sensitive information under the guise of refunds or order issues. A separate industry report reinforces the same operational pattern: attackers increasingly rely on **valid credentials** and trusted collaboration tools rather than software exploits, with cloud identity compromise driving most investigated incidents and some intrusions using **Microsoft Teams voice phishing** and **Quick Assist** to gain access, move laterally, and deploy ransomware. Other references in the set cover different stories entirely, including the **CamelClone** espionage operation, a **FancyBear/APT28** infrastructure exposure, and a general weekly security recap, and do not describe the same phishing activity. This is **not fluff** because the relevant items contain substantive threat intelligence on active attack methods, delivery infrastructure, and attacker tradecraft.
1 months ago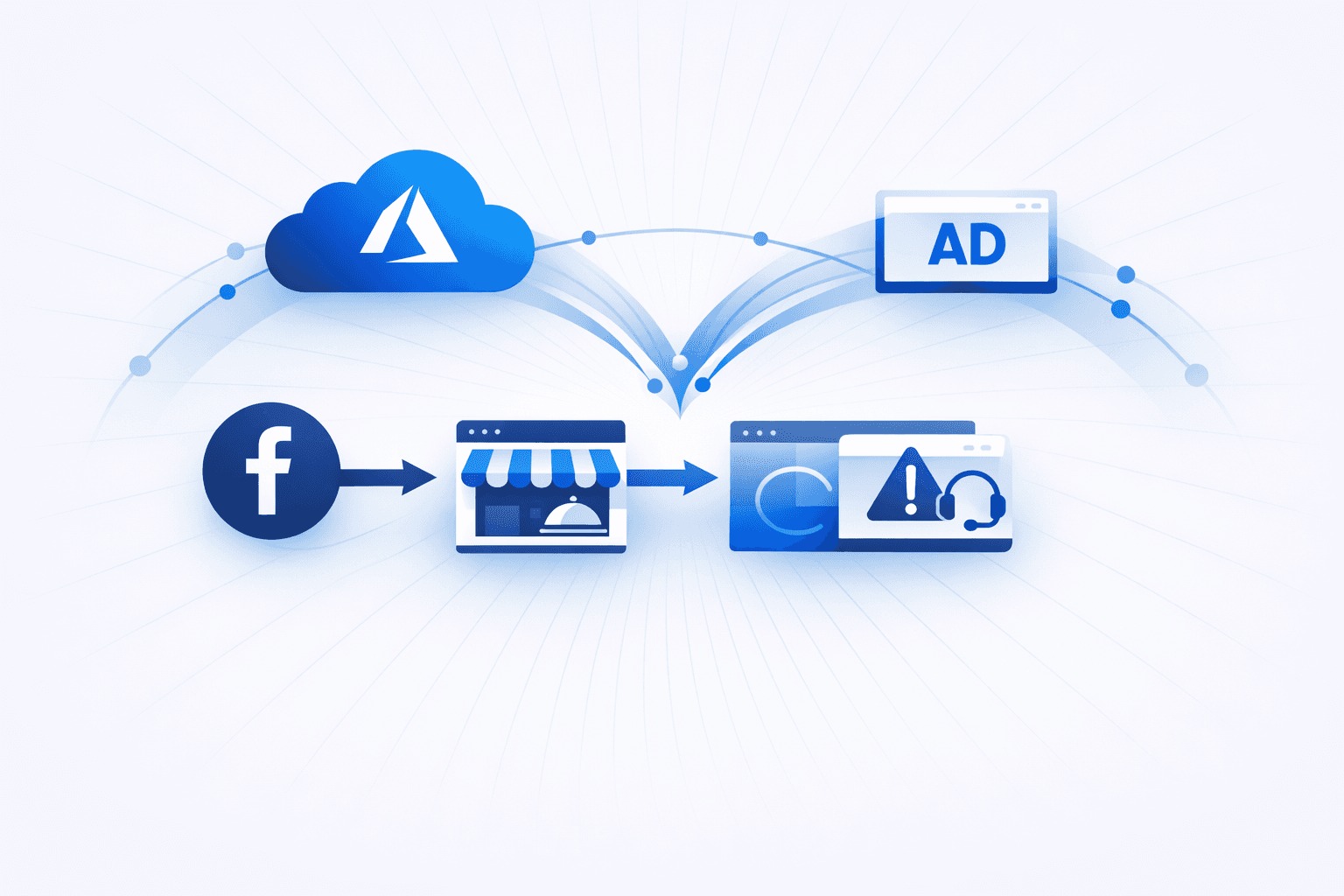
Threat Actors Abuse Trusted Cloud and Ad Platforms for Multi-Stage Phishing and Scam Delivery
Threat actors are increasingly using **trusted platforms**—including cloud hosting and major ad networks—to deliver multi-stage phishing and scam campaigns that evade traditional URL and domain reputation controls. Recent activity includes a **three-step malvertising chain** delivered via **Facebook paid ads** that redirects victims through a decoy site (e.g., a fake Italian restaurant page) before landing on a **tech support scam (TSS) kit** hosted on **Microsoft Azure** infrastructure (including `web.core.windows.net`). Researchers reported rapid infrastructure churn, with **100+ domains rotated in seven days**, and targeting focused on **U.S. users** with activity concentrated on weekdays. Parallel enterprise-focused campaigns are hosting phishing infrastructure on **Microsoft Azure Blob Storage**, **Google Firebase**, and **AWS CloudFront**, using **redirect chains, CAPTCHA gates, and QR codes** to bypass automated analysis and email defenses. Analysis highlighted the use of **Adversary-in-the-Middle (AiTM)** phishing-as-a-service kits—**Tycoon2FA**, **Sneaky2FA**, and **EvilProxy**—to steal credentials and **session tokens** even when MFA is enabled. Separately, researchers documented a “clean email” approach to steal **Dropbox** credentials: benign-looking procurement-themed emails deliver **PDF attachments** that hide clickable elements (e.g., via *AcroForms* and `FlateDecode`), which then route victims to a second-stage file hosted on **Vercel Blob** and ultimately to a fake Dropbox login page that captures credentials and collects victim telemetry (IP address, location, and device details).
1 months ago
Phishing Campaigns Abuse Trusted Platforms and Legitimate Workflows to Evade Detection
Multiple campaigns are abusing *legitimate* cloud and platform workflows to make phishing and fraud harder to detect. Attackers are generating real Apple and PayPal invoice/dispute emails and embedding scam phone numbers in user-controlled fields (e.g., “seller notes”), resulting in messages that carry valid **DKIM** signatures and originate from high-reputation domains; this “**DKIM replay**” style abuse bypasses many email controls because authentication validates the sender domain, not the safety of the embedded content. In parallel, threat actors are leveraging free **Google Firebase** developer accounts to host brand-mimicking phishing pages on trusted `firebaseapp.com` / `web.app` subdomains, increasing delivery and click-through rates by exploiting domain reputation and common allowlisting of Google infrastructure. A separate but related social-engineering technique targets **Telegram** users by manipulating Telegram’s official authentication workflows to obtain fully authorized sessions rather than simply stealing passwords. Victims are lured to Telegram-lookalike pages (often on ephemeral domains) that prompt QR scanning or phone-number entry; user interaction triggers a real login attempt initiated by the attacker, and once the victim approves the authorization prompt on their device, the attacker gains persistent account access and can pivot to follow-on attacks via the victim’s contacts. These incidents collectively highlight a shift toward “living off trusted services,” where adversaries avoid compromising vendors and instead weaponize legitimate features, trusted domains, and sanctioned authentication flows to reduce detection and increase victim compliance.
1 months ago